Search Results
You searched for: cybersecurity
Business leaders know they must prepare for technological upheavals in the years ahead. But keeping up-to-date on new technologies—to say nothing of understanding their complexities and forecasting those shifts—is an […]
We've got five great eBook bundles that can get you working in five of the hottest tech fields around, all at a fraction of their original price.
The recent discovery highlights an alarming cybersecurity vulnerability in the health care industry.
Break into the lucrative world of tech with training you can do anywhere.
Pandemic-inspired housing innovation will collide with techno-acceleration.
Fifty years ago at UCLA, the first message was sent over the predecessor to the internet.
▸
with
Stock markets may be plummeting, but that doesn't mean the spread of COVID-19 is hurting everyone's bottom line.
Cybercriminals have a wide variety of motivations for their attacks, and, correspondingly, there are a wide variety of targets. While few of us will find ourselves in positions where we […]
If AIs can generate photos of people who don't exist, what else can they imagine?
As it turns out, hacking an election isn't as hard as you'd think.
The social media company's recent transparency report claimed that it had taken down a staggering number of fake accounts — but it's unlikely they're catching them all.
Flattening the curve on panic and disinformation.
Michael Dowling, Northwell Health's CEO, believes we're entering the age of smart medicine.
The FBI has warned banks that a group of criminals might be planning a large-scale ‘ATM cash-out’ after receiving a tip from an unknown source.
The short answer is that an exact copy of the website was hacked, yes. In just 10 minutes. By an 11-year-old kid.
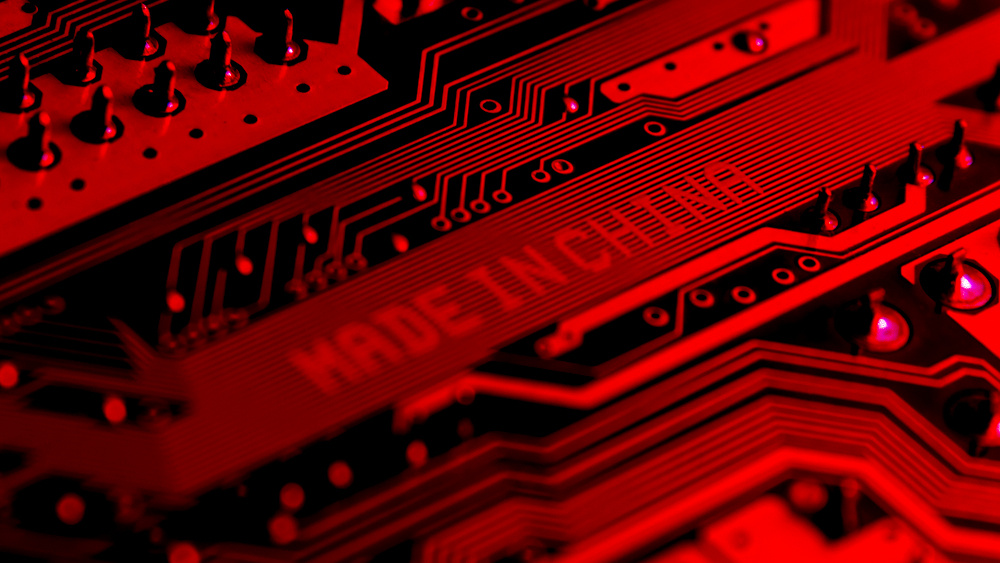
A new report from Bloomberg describes how Chinese subcontractors secretly inserted microchips into servers that wound up in data centers used by nearly 30 American companies.
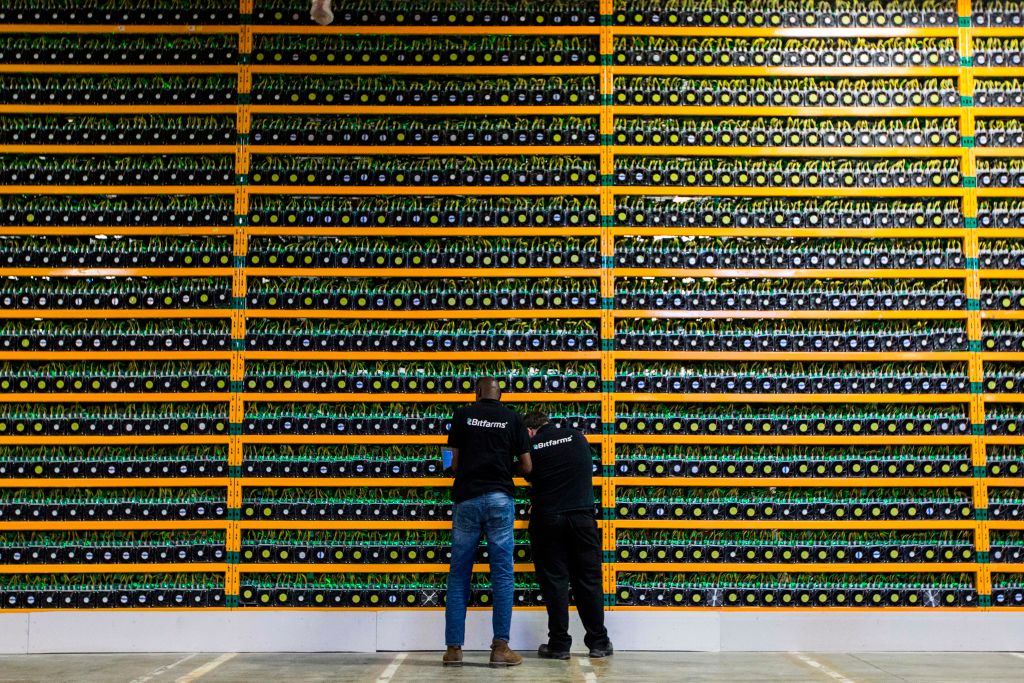
Cybersecurity costs billions of dollars each year. Building on a blockchain could solve many of our security problems.
Chinese hackers at DEFCON have demonstrated how they were able to hack an Amazon Echo unit, enabling them to listen and record unsuspecting targets.
Catch up on the phenomenon known as ASMR, which is exploding in popularity and may be linked to the appeal of religion.
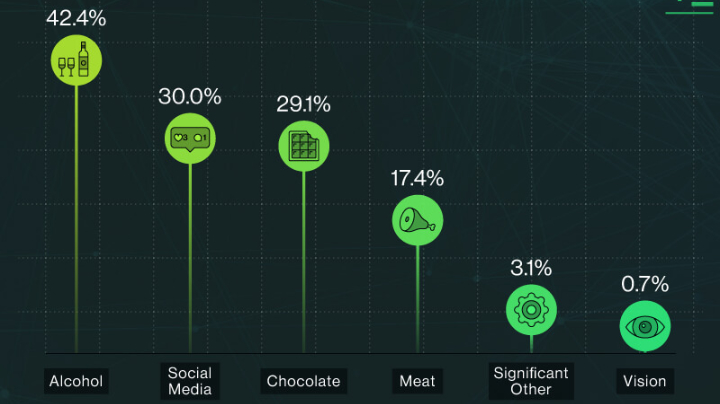
Infographics show our attitudes about privacy and keeping our data secure online.
DEFCON hackers find it’s really easy to hack U.S. voting machines.
Your Internet Service Providers are collecting and selling your browsing history. Does that bother you? If so, it may be time to setup a Virtual Private Network (VPN) to better encrypt your data and spoof your location.
Pay your bills, slip through security, and take a train, all without fumbling through your wallet.
Charges of treason are often used incorrectly in today's political climate. Treason has a very specific definition in the U.S. Constitution.
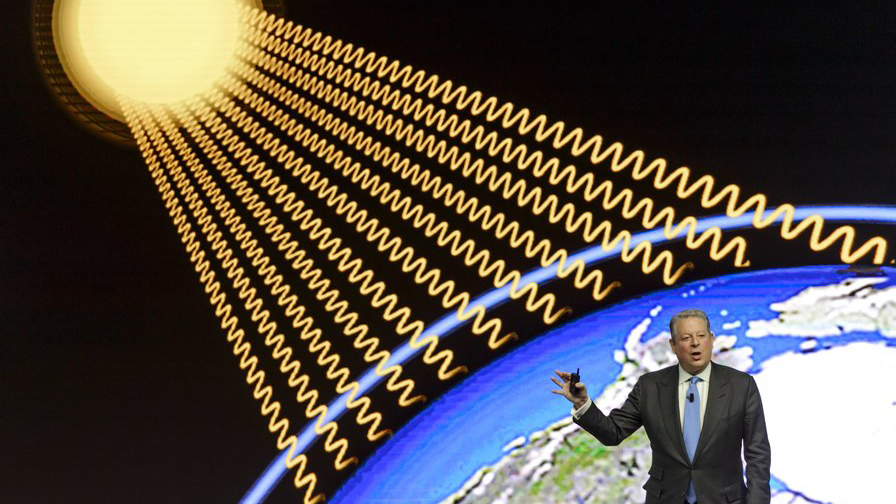
Is it good science in practice or just a smokescreen?
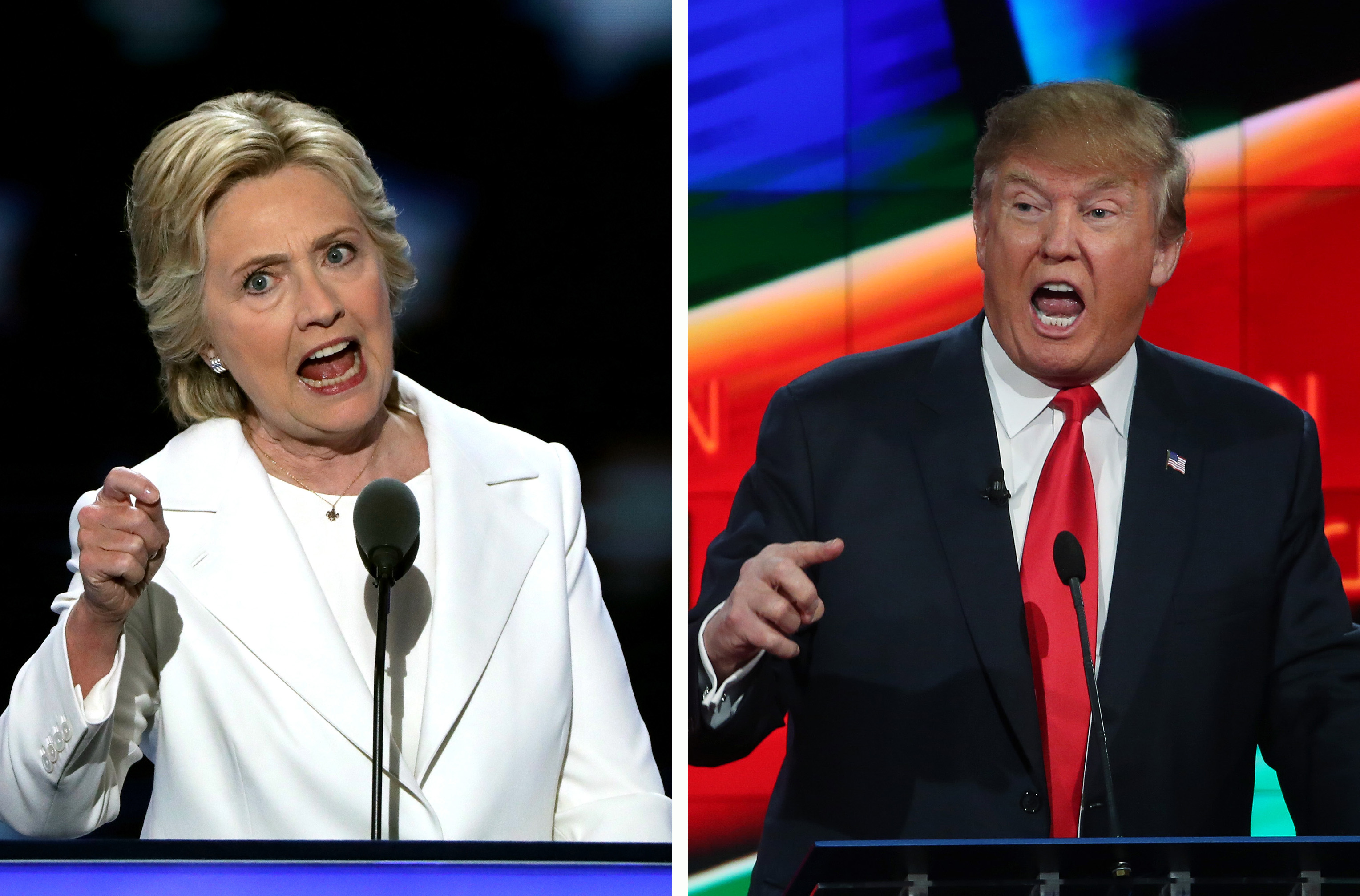
ScienceDebate.org sent 20 fine-tuned questions to the presidential candidates. 3 out of 4 of them responded. Here's where they stand on key science issues.
The FBI issued a PSA this week warning us of how hackers can take control of our cars. Its time for a software upgrade.
Ever wonder what happens when your credit card number, Google credentials, and online banking password get stolen?
Online voting will transform our political process. It will improve turnout and make the U.S. a more democratic society.