Columbia study finds new way to extract energy from black holes
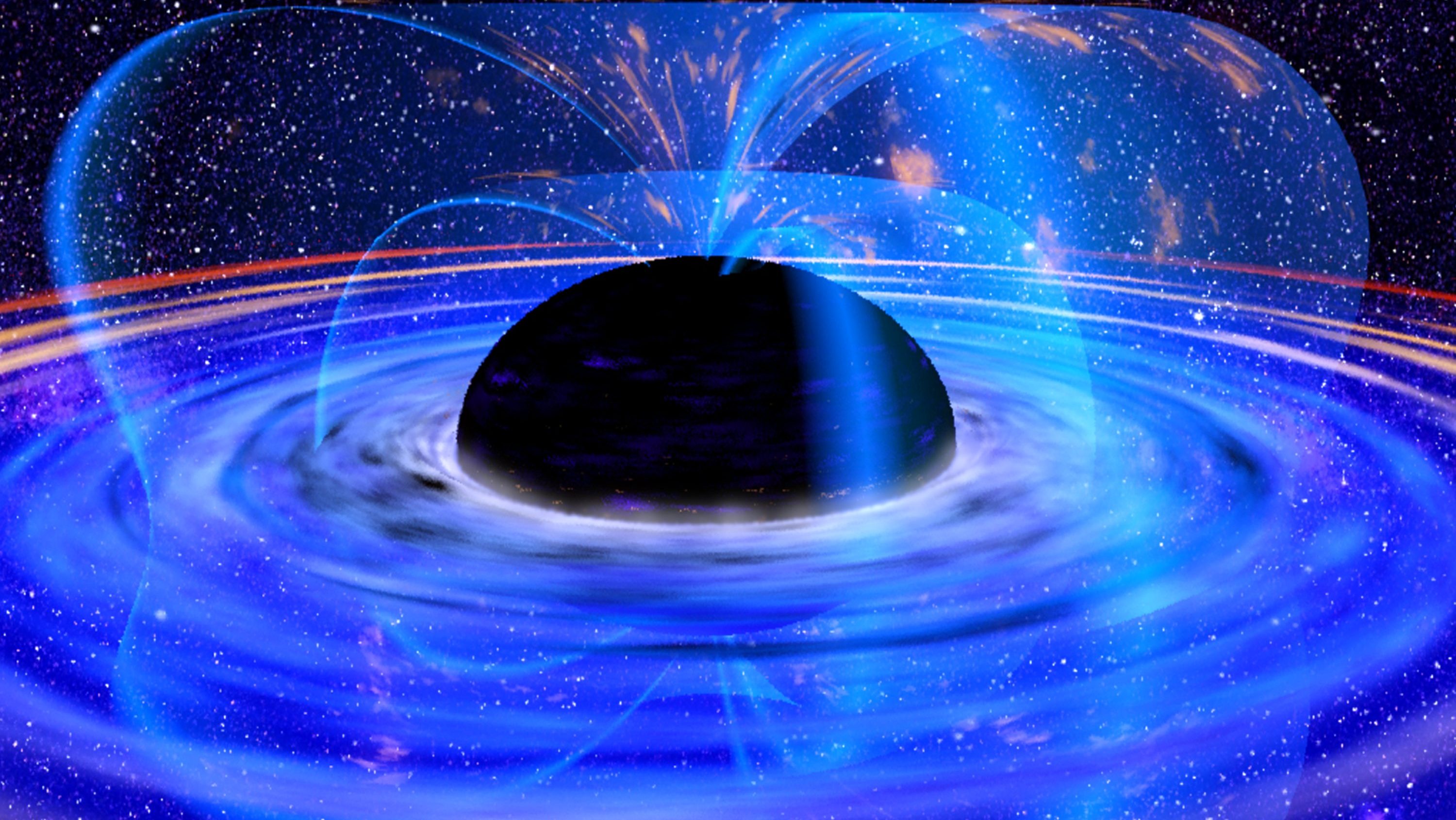
Credit: NASA's Goddard Space Flight Center
- In 1969, the physicist Roger Penrose first proposed a way in which it might be possible to extract energy from a black hole.
- A new study builds upon similar ideas to describe how chaotic magnetic activity in the ergosphere of a black hole may produce vast amounts of energy, which could potentially be harvested.
- The findings suggest that, in the very distant future, it may be possible for a civilization to survive by harnessing the energy of a black hole rather than a star.
Like the Sun, the stars scattered throughout our Milky Way and beyond produce unfathomable amounts of energy. But so, too, do the objects we can’t see: black holes.
For decades, scientists have wondered whether it’s possible to extract energy from black holes, which are the mysterious regions of spacetime that form when stars collapse into themselves. Siphoning energy from these areas of ultra-condensed matter could provide a virtually endless power supply for deep-space civilizations, if physically and practically possible.
While undoubtedly the stuff of science fiction, the idea is far from new.
In 1969, the physicist and Nobel Laureate Roger Penrose proposed it might be possible to extract energy from a rotating black hole. He thought this could occur in a black hole’s ergosphere.
The ergosphere is a region just outside a black hole’s event horizon, the boundary of a black hole beyond which nothing, not even light, can escape. But light and matter just outside the event horizon, in the ergosphere, would also be affected by the immense gravity of the black hole. Objects in this zone would spin in the same direction as the black hole at incredibly fast speeds, similar to objects floating around the center of a whirlpool.
The Penrose process states, in simple terms, that an object could enter the ergosphere and break into two pieces. One piece would head toward the event horizon, swallowed by the black hole. But if the other piece managed to escape the ergosphere, it could emerge with more energy than it entered with.
The movie “Interstellar” provides an example of the Penrose process. Facing a fuel shortage on a deep-space mission, the crew makes a last-ditch effort to return home by entering the ergosphere of a blackhole, ditching part of their spacecraft, and “slingshotting” away from the black hole with vast amounts of energy.
In a recent study published in the American Physical Society’s Physical Review D, physicists Luca Comisso and Felipe A. Asenjo used similar ideas to describe another way energy could be extracted from a black hole. The idea centers on the magnetic fields of black holes.
“Black holes are commonly surrounded by a hot ‘soup’ of plasma particles that carry a magnetic field,” Comisso, a research scientist at Columbia University and lead study author, told Columbia News.

Ergosphere representationYukterez (Simon Tyran, Vienna)
In the ergosphere of a rotating black hole, magnetic field lines are constantly breaking and reconnecting at fast speeds. The researchers theorized that when these lines reconnect, plasma particles shoot out in two different directions. One flow of particles shoots off against the direction of the spinning black hole, eventually getting “swallowed” by the black hole. But the other flow shoots in the same direction as the spin, potentially gaining enough velocity to escape the black hole’s gravitational pull.
The researchers proposed that this occurs because the breaking and reconnecting of magnetic field lines can generate negative-energy particles. If the negative-energy particles get “swallowed” by the black hole, the positive particles would theoretically be exponentially accelerated.
“Our theory shows that when magnetic field lines disconnect and reconnect, in just the right way, they can accelerate plasma particles to negative energies and large amounts of black hole energy can be extracted,” Comisso said. “It is like a person could lose weight by eating candy with negative calories.”

Black holeEvent Horizon Telescope Collaboration
While there might not be immediate applications for the theory, it could help scientists better understand and observe black holes. On an abstract level, the findings may expand the limits of what scientists imagine is possible in deep space.
“Thousands or millions of years from now, humanity might be able to survive around a black hole without harnessing energy from stars,” Comisso said. “It is essentially a technological problem. If we look at the physics, there is nothing that prevents it.”