Sign up for Big Think on Substack
The most surprising and impactful new stories delivered to your inbox every week, for free.
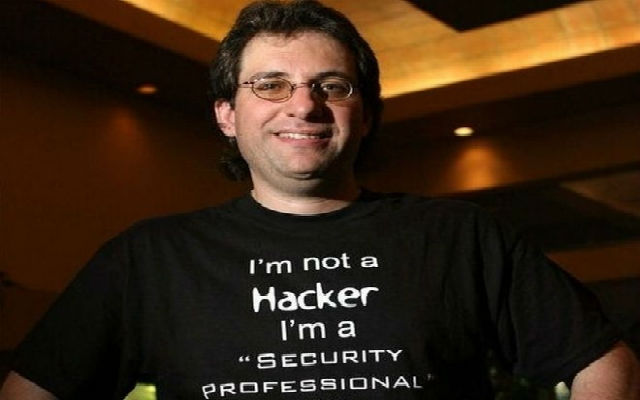
In this clip from our recent interview, Kevin recalls an incident back in 1981 when he was seventeen: He and a phone-phreaker buddy decide to sneak into Pacific Telephone’s central office in Hollywood. They social-engineer the key code and stroll in nonchalantly. Almost immediately, a security guard catches them. Typically this kind of story ends with a weeping phone call to mom. But Kevin Mitnick was not your typical seventeen-year-old . . .
Kevin Mitnick: I was about, you know, 17 years-old and I was in Hollywood at the time with another phone phreaker friend, and we decided we’re going to go take a self tour of the Sunset Gower Central Office. We wanted to look at the switching equipment, maybe we can come across some passwords or dial-up numbers to gain access to the system from the outside. So we actually acquired the door code to get into this building, and we’re like, it’s a nine-story building. . . . So we’re walking through. We’re looking at the cool equipment. We weren’t going to steal anything. We weren’t going to take any equipment out of there. We just wanted to see how everything worked.
And about 20 minutes into our self-guided tour this big security guard was there, and he goes “Hello!” And we look over, “Yes?” “Who are you?” “Well my name is Steve. I’m from the Cosmos Center in San Diego. I'm showing my friend the Central Office. He’s never seen it.” “At 2:30 in the morning?” “Well, you know, we were in Hollywood seeing a movie and I figured after the movie I could show it to him . . . and that it was just the timing of everything.” He goes, “Let me see your ID.” “Hold on. Yeah, no problem sir.” I'm reaching into my pocket. I reach into the other pocket. I go, “I must have left it in my car. I'll go get it. I'll be right back.” He goes, “No, you’re both coming with me.”
So he escorts us up to the ninth floor security and he goes, “I just caught these guys in the building and this guy claims he works with the Cosmos Center in San Diego.” I said, “Yes, I do.” “I work in the Cosmos Center in San Diego.” And I go through the whole story again, and I already knew the supervisor of that center. I just knew it from my phone phreaking experience, and they said, “Well we’re going to go ahead and call your supervisor to verify that you’re legitimate.” I go, “No problem. Go ahead. You can call Sally whatever.” So they actually had an inner company directory, a paper book. They looked up her home number . . . and I'm saying, “Listen guys. It’s 2:30 in the morning. You’re going to wake my boss. She’s going to be really pissed.” And, “No, we’re going to verify who you are.”
So they called the supervisor, woke her up and they go, “Yeah, we have your employee Steve here in the Hollywood Gower Office. We caught him in the building with some other guy and we just wanted to make sure he is with you.” And then I said to the guy, I go, “Why don’t you let me talk to her?” So they hand the phone to me, and I press the phone really tight to my ear so they can’t hear. I go, “Hey Sally, it’s Steve. How are you doing? Yeah, I'm sorry they woke you up.” As I'm talking to her calmly and nicely she’s going, “Who is this? Who are you? Who are you?” “Yeah, well I'm really sorry this happened. Are we still on for lunch on Tuesday? Oh, we are? Well, I do have that report almost done. It will be on Thursday.” And she’s going, “Who are you? Who is this? Who is this?” And I'm holding the phone really tight to my ear so they can’t hear what she is saying, and then I said, “Okay, well I'm sorry about the interruption. Go back to sleep. See you on Tuesday.” And then I go, “Satisfied?” and I hang up the phone. And then there . . . there’s a lot—you could see the uncomfortable silence of I didn’t hand the phone back. But I said, “Are you satisfied?” And he goes, “Okay.” I said, “We’re going to be only about 15 more minutes. We’ll be out of the building. We’re sorry we caused this problem.”
We didn’t decide to stay 15 more minutes. We went immediately to the lobby and ran out, and then we sat in my car about a block away just to look at the front door for awhile. And like 20 minutes later that same guard came out. He is looking in both directions. So it was a way I was able to use social engineering to get myself out of a bad predicament.
Directed by Jonathan Fowler
Produced by Elizabeth Rodd