This Map Shows Us Why Tor Is so Important

If a person wanted to keep their movements online private, I would recommend they use Tor. It’s an anonymity tool that has been used by many different kinds of people (for many different purposes). It’s the browser of choice for whistle-blower Edward Snowden, and one of the easiest ways to protect your privacy online.
The project relies on a number of volunteer relays set up all across the world. At a glance, Tor looks very much like you’re browsing in Firefox. However, underneath, its software is working to mask your identity and location (to a point) by bouncing your signal across the globe. By the time the signal comes out the other end, advertisers and websites won’t see your computer browsing their site from the United States — they may see a computer browsing from the Netherlands.
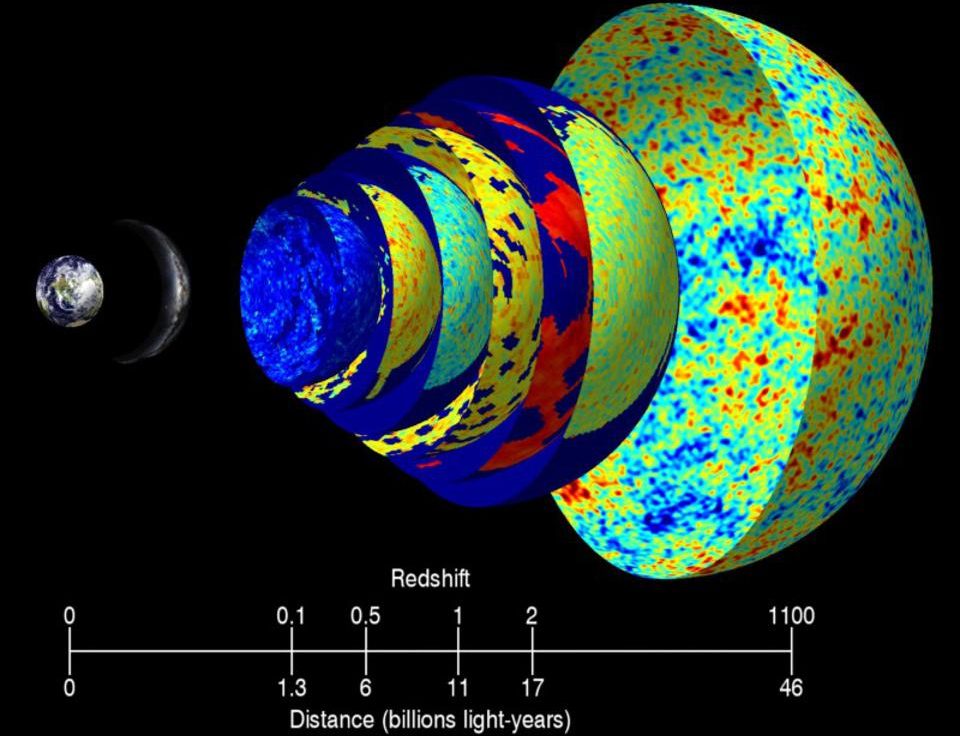
Uncharted used publicly published data from the Tor project to create an interactive map, showing the beauty and complexity of Tor’s expanding network of anonymous users.
So, how does information flow between relay servers? Like this:

TorFlow isn’t a live analysis of Tor’s traffic. But it allows anyone to run simulations based on the date. Depending on the day, these simulations will begin to tell a story about the rise of Tor and the important role it played in movements across the world.
“The whole point of the Tor network is to remain anonymous,” David Schroh, a software engineer at Uncharted, said to Wired. “But by visualizing it, can you see patterns you wouldn’t expect.”
The map shows how much the infrastructure of the Tor network has grown over the years from a U.S.-based project to a global initiative that has grown tremendously in Europe. But it shows how important it is to protect anonymity, and why Tor needs to exist. Just click on Egypt, where you’ll see spikes in Tor’s use during the Arab Spring protests in 2011 and again after the political coup in 2013.

***
Photo Credit: TorFlow