hacking
As a form of civil disobedience, hacking can help make the world a better place.
Opportunistic agility is running rampant among hackers and scammers.
Protect yourself and your personal information at all times on the internet.
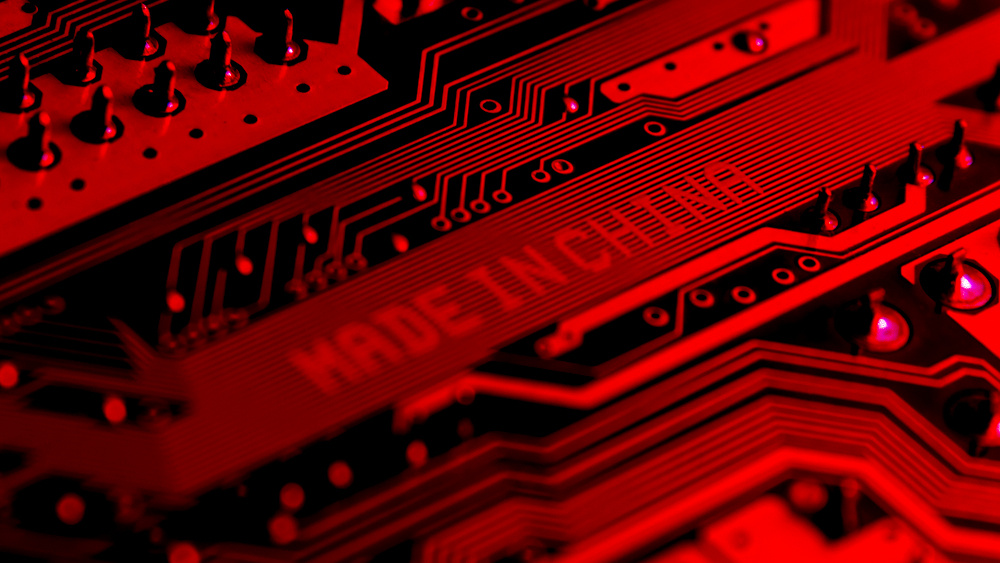
A new report from Bloomberg describes how Chinese subcontractors secretly inserted microchips into servers that wound up in data centers used by nearly 30 American companies.
Getting your vote to where it matters can be harder and more corrupt than it should be. Could blockchain technology build a better system and rebuild people’s trust?
▸
3 min
—
with
KGB-era “active measures” are still being used by Russian intelligence agencies today, according to experts.
The work of Kremlin-approved philosopher Alexander Dugin provides key insights on the longterm strategy behind Russian hacks of the American elections.