cybersecurity
Opportunistic agility is running rampant among hackers and scammers.
Just because your team has gone remote doesn’t mean you need to be vulnerable to hacks, breaches, and scams.
Video meetings on the popular platform don’t seem to offer end-to-end encryption as advertised.
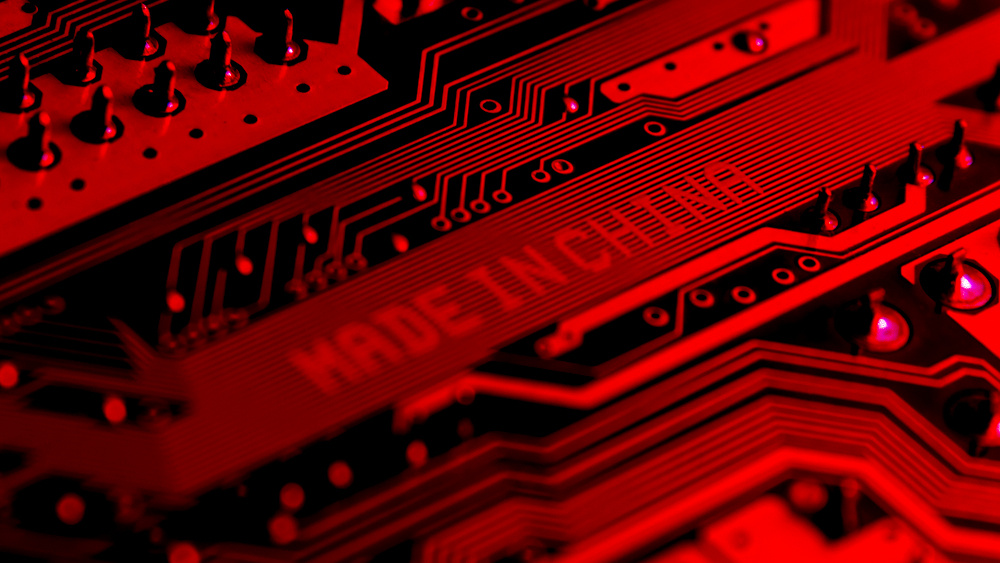
A new report from Bloomberg describes how Chinese subcontractors secretly inserted microchips into servers that wound up in data centers used by nearly 30 American companies.