New cyberattack method steals data directly from power cords and grids

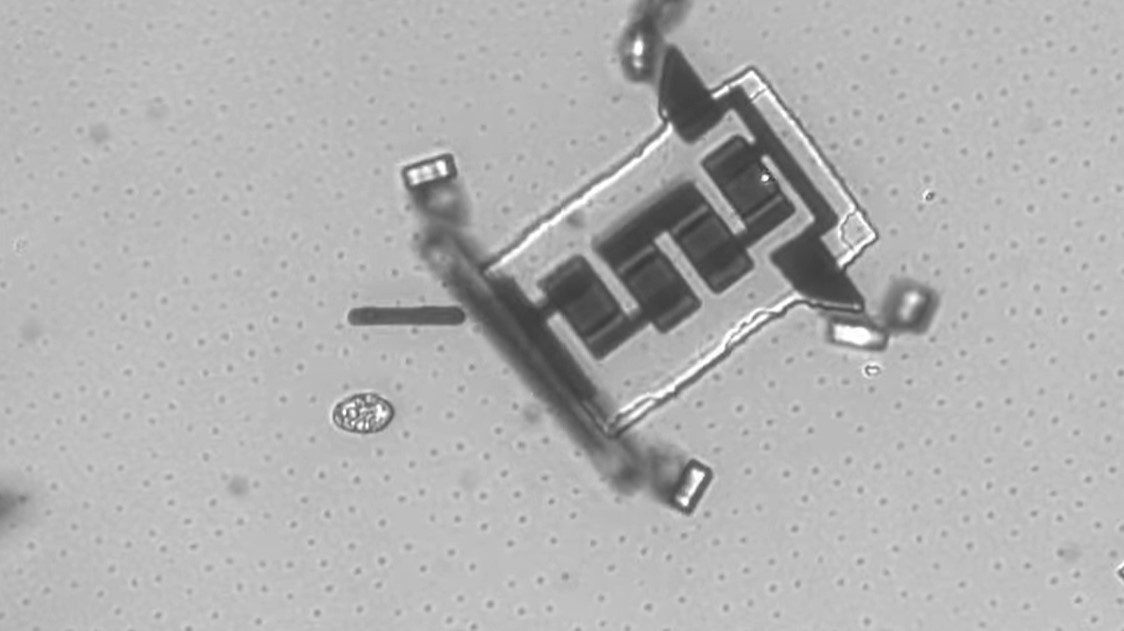
Sometimes, sensitive computers are removed from the main network and isolated into what’s known as a Faraday Cage, which is part of an ‘air gap’—literally, moving the computer in question away from anything connected to the world.
Breaching these networks requires the installation of malware on the host computer, but once that’s accomplished the possibilities are there; it’s already been proven to work with low-level magnetic fields.
As Tech Republic wrote in early 2018, new cyberattack methods use a “low-level field that allows attackers to covertly access any device with a CPU hidden inside a Faraday cage or air-gapped room. That’s worth reiterating: Anything with a CPU can be manipulated using what Guri and his team call the Odini method.”
Basically, malware can infect the CPU to influence what parts of it are actually performing processing, which then changes the low-level magnetic waves coming out of the computer. Data is “piggy-backed” onto the magnetic waves, and—presto!—it can be picked up by a device designed to receive that magnetic field information and compile the data. A second method, dubbed Magneto, does effectively the same thing, but via simple smartphone.
The latest technique, called PowerHammer, exploits some of the same concepts—but via the power lines that keep the computer running.
Incredibly, the data can be compromised via direct power line connection, and—at a much slower rate—via the grid itself.
Mordechai Guri, lead author of the PowerHammer paper linked above, explains: “The data is modulated, encoded, and transmitted on top of the current flow fluctuations, and then it is conducted and propagated through the power lines. This phenomena is known as a ‘conducted emission’. We show that a malicious code can influence the momentary power consumption of the computer, generating data-modulated conduction on the power lines in the low-frequency band. The generated noise travels along the input power lines and can be measured by an attacker probing the power cables.”
So, for the ultimate in security, pretty much a solar-powered computer surrounded by a series of metal-encased, magnetically resistant boxes… buried under the sea?
Or perhaps on top of a mountain.
Here’s a bit more about Faraday cages, named after—you guessed it—Michael Faraday.