An All-Star Panel on Cybersecurity

The former Chairman of the Joint Chiefs of Staff, Admiral Mike Mullen, characterized “cyber” as an “existential threat to the United States of America” in a recent issue of Fortune Magazine:
The challenge for me and many other leaders is to really understand it….We are vulnerable in the military and in our governments, but I think we’re most vulnerable to cyberattacks commercially. This challenge is going to significantly increase….The potential is to shut down our transportation system, shut down our banking system, shut down other infrastructure in our country, and essentially bring us to parade rest.
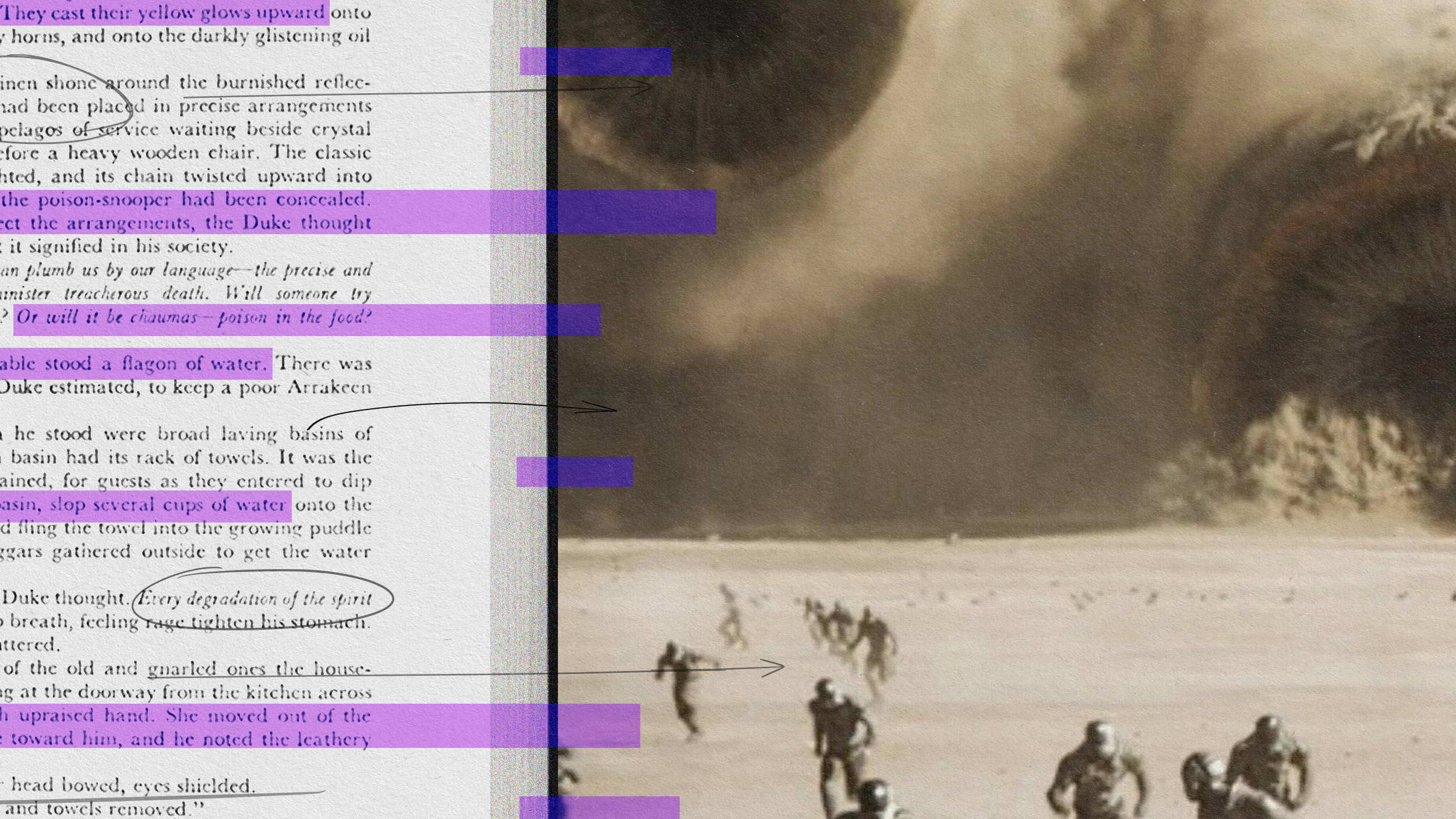
Shortly after he made that statement, we learned about Flame: a 20-megabyte computer virus that contains 20 times more code than the much-discussed Stuxnet virus, it evaded detection for five years and, according to researchers at the Kaspersky Lab, could have infected over a thousand computers across the Middle East. Flame has fanned the flames (I couldn’t resist) of the debate over cybersecurity: while the Washington Post just ran a special report, “Zero Day: The Threat in Cyberspace,” ABC News investigative producer Lee Ferran argues that “human carelessness” is more responsible for cyberthreats than technical advances: “no matter how sophisticated the attack or how capable the defenses, the weakest link in cybersecurity is often the human at the keyboard.”
So how worried should we be? To analyze Admiral Mullen’s argument—and consider issues of cybersecurity more broadly—I spoke to several leading figures:
- Jeffrey Carr, CEO of Taia Global, Inc.
- Mikko Hypponen, chief research officer at F-Secure
- Herbert Lin, chief scientist with the National Academies’s Computer Science and Telecommunications Board
- Chris Roosenraad, co-chairman of the Messaging, Malware, and Mobile Anti-Abuse Working Group
- Bill Woodcock, research director at Packet Clearing House
- Ethan Zuckerman, director of MIT’s Center for Civic Media
Here are my takeaways:
- It’s important to deconstruct cyberthreats into a spectrum of threats, rigorously analyzing each on the basis of its likelihood and impact.
- How one assesses the risks of those threats depends in part on one’s willingness to extrapolate: that is, to infer from that which we can observe and verify that there’s much more occurring that we can neither observe nor verify. Recall former Secretary of Defense Donald Rumsfeld’s distinction between “known knowns,” “known unknowns,” and “unknown unknowns.”
POWER GAMES: How would you respond to Admiral Mullen’s statement?
ARQUILLA: Cyberattack, at its worst, poses the threat of “mass disruption.” This could prove costly, in economic terms, and could lead to battlefield losses if the information systems upon which our troops rely are disrupted in the middle of a fight. But all this pales in comparison to the threat posed by weapons of mass destruction—nukes, bugs, and poisons. Cyber is bad, but does not pose an “existential threat.”
CARR: I partially agree…No one has produced an accurate threat assessment on this topic, so Admiral Mullen isn’t really speaking from a base set of verifiable facts. What he describes is more of a potential threat on a broad scale. If, on the other hand, he focused solely on the threats to specific industries like defense contracting, energy, artificial intelligence, research and development, and other specific high-value sectors, I’d agree with him 100%.
LIN: It depends on what you mean by “existential.” An existential threat is one that, if not countered, could threaten the existence of the United States as we know it today…In the short term, is there a cyberthreat that could threaten the existence of the United States as we know it today? Sure. Imagine a powerful nuclear electromagnetic pulse weapon detonated above the horizon of much of the United States. Such a weapon could totally fry most of the existing electronic infrastructure (that is, all computer and communications technology, both standalone and embedded in devices) on which we rely today. Such a weapon might shut down the nation’s power grid and damage much of our ability to recover.
In the long term, is there a threat that could threaten the existence of the United States as we know it today? Sure, and it does not even have to be a cyberthreat. The United States has the world’s dominant economy today, and exerts enormous economic power and influence around the world….such leadership cannot be taken for granted, and we do have economic competitors today….A threat to U.S. economic dominance could be regarded as existential, and there I would say that the United States does face an existential threat in the long run [from China].
Cyber, of course, plays into this threat: economic espionage against the United States gives other nations advantages over us in any economic competition, and we know that much of the economic espionage against us is committed using cyber means. The notion that cyber plays into an economic threat against the United States is consistent with Admiral Mullen’s statement…that “we’re most vulnerable to cyberattacks commercially.” On the other hand…the United States does not conduct espionage against other nations for the benefit of private U.S. companies. So to some extent, we have chosen to tie one hand behind our backs. There are other scenarios that are sometimes offered, such as a cyberattack that shuts down the U.S. electric power grid for months at a time. That would be a very bad outcome, and is also arguably [an] existential [threat]. But…there are two relevant points. First, this would be very hard to do….Second, there are other, non-cyber ways to achieve the same effect, and the key point here is that we don’t do very much to protect against those other non-cyber ways either.
RID: Unless he comes forward with more detail, which I frankly doubt he can—either because he doesn’t have it or, far less likely, because it’s classified—I would dismiss this statement.
ROOSENRAAD: My main response…is to nod and wonder what took the U.S. military this long to acknowledge the importance of the Internet. The Internet has become a critical part of the world economy, and that obviously means the U.S. economy as well. The purpose of the U.S. military is to protect the country’s interests around the world, so it’s inevitable that they’ll look to do so on the Internet….From a state-versus-state point of view, I agree [that “[t]his challenge is going to significantly increase”].
Over the last few years, we’ve seen a rather radical change in the world of online malware, bots, and other threats that has grown from individuals into gangs and now into…a whole shadow economy, with criminals and criminal gangs that specialize in specific areas. One expects that state-backed activities will similarly evolve from individual actions into large-scale programs, with strategic goals, centralized programs, large budgets, and other conventions….Admiral Mullen is right that commercial entities are being attacked, but I’d contest the statement that industry as a whole is more vulnerable than the military or the government. While industry approaches to cyberprotection vary from company to company, I think you’ll find that many large corporations are quite far along with their defenses against attacks, since they are aware that companies are being attacked every day.
WOODCOCK: There are two factors that make the United States particularly vulnerable to cyberattacks. First is the degree to which we, as a country, are willing to make enemies of arbitrary people in random parts of the world, for no reason or gain….Second, for us, cyber is an asymmetric risk. That is, we have far more to lose in a cyberconflict than most countries do, because so much of our economy is dependent upon the Internet…By militarizing cyberspace, we place at risk something that we hold dearer than do our adversaries. I remember thinking this when we used the BLU-114 graphite fiber bombs [according to GlobalSecurity.org, “special-purpose munition[s] for attacking electrical power infrastructure”] in Bosnia: it might have been painful for them, but it would have been utterly crippling if it had been used in the U.S., and it was an idea that we really shouldn’t have put out in the world. And, of course, all of this affects us commercially. The Internet is private-sector.
ZUCKERMAN: Many of the doomsday scenarios that are cited fail to distinguish between Internet-based systems and non-Internet-based control systems. The Stuxnet worm was the first clear piece of evidence that attacks could cross that barrier. It was a “proof of concept,” but not the norm. In fact, it was a pretty clever, even miraculous, attack….I’m scared of DDoS [distributed denial-of-service attacks] and malware, and a little less scared of the possibility that people will break the barrier that I mentioned earlier. We should spend more time being scared of that which we know is happening than that which could theoretically be happening.
When computer-security folks say that they see little justification for the doomsday scenarios, military officials often respond: “You don’t know what’s out there.” I call that response “security through obscurity.” How are we supposed to respond if we can’t see the evidence—if there even is evidence—for the dire threat assessments? The reality is that the Internet has more or less worked even though it has enormous insecurities. As recently as a decade ago, some people seriously thought that it would collapse under the weight of spam. Then it was phishing [attempts to steal sensitive information over e-mail by pretending to be a trustworthy source] that would be an apocalypse. The truth is that there are gangs of geeks out there working very hard to fix the Internet’s security gaps. They get very little press, partly because they don’t seek it, and partly because it’s sexier to say that the sky is falling than to say that we’re chipping away at those gaps.
PG: Why do assessments of cyberthreats vary so significantly among analysts? While some argue that those threats are serious and poised to increase, others contend that they’re exaggerated and well within our ability to manage.
ARQUILLA: Those who see less of a threat tend to view the absence of a “Digital Pearl Harbor” as a sign that it is unlikely that there will ever be one. Others of us (I am one of them) look at actual vulnerabilities—as demonstrated in real-world events and rigorous exercises—and worry that thinking enemies will soon make the virtual domain a theater of war and target for terror.
CARR: Because most of them occur below the radar. Most companies have no idea that they’re losing data or have unauthorized users crawling their networks. So we extrapolate…from what we do discover to cover those [threats] that we presume must also be happening which haven’t been discovered. That’s fine if the person making the estimate sticks to high-value industries, but often that’s not the case. Instead, people see something in the news about China, and all of a sudden EVERYTHING is about China. Or they read about a high-profile cyberattack and extrapolate from that that ALL companies have been breached. That’s a completely inane point of view, but the media eats it up because it makes for an exciting headline and expanded readership.
LIN: I’d argue that both kinds of analysts are right. That is, cyberthreats are serious and poised to increase, but…they are (sometimes) exaggerated and well within our ability to manage. Whether they are within our WILL to manage is a different point. For all of the expressed concern about cybersecurity, few people seem to be willing to pay very much (in dollars or effort or convenience) to fix those problems. If we as a nation would actually implement what we have the knowledge and the technology to do, our cybersecurity posture would be much stronger than it is now.
WOODCOCK: The future is unknowable, and people are very bad at quantifying risk. Some people consider what’s possible, while others consider what’s likely. Some people think that what’s possible will happen eventually, while the temporally egocentric assume that anything that’s possible will occur while they’re alive. Personally, I’m an optimist, and believe that people are, by and large, good, and it doesn’t occur to them to actually do the terrible things that other people know are possible. Perfect security is impossible, yet planes and buildings are not blowing up, because most people are rational and well-intentioned most of the time, and it’s neither nice nor useful to blow up planes. I think there are many more inventive, pessimistic, paranoid people than there are inventive, sociopathic, motivated people. Thus, people invent and worry about scenarios that are far worse than any that will actually be carried out in our lifetimes.
PG: When individuals discuss cyberthreats, to what are they generally referring? Cybercrime? Cyberattacks? Cyberterrorism? Cyberwar? How important are the distinctions between those categories?
ARQUILLA: Cyberwar has many faces. “Cybotage” can be used to gum up the works—think Stuxnet. Cybersnooping is a key aspect of modern intelligence, as is industrial espionage, the latter being a cause of the hemorrhaging of American intellectual property today. Cyberwar has made an appearance on the battlefield—think the Russian use of cyberattacks on Georgia’s information systems during the 2008 war, which contributed to the quick overrun of the latter’s forces in the field. Terrorists haven’t yet gotten up to speed in the cyber realm, probably because it takes time to develop top-flight hackers, and terrorists are reluctant to recruit cyber mercenaries (they might be working for us, like the double agent who infiltrated the Al Qaeda cell in Yemen).
CARR: There are two big categories of cyberthreats: cybercrime against banks and cyberespionage against high-value industries. Much rarer are acts of cyberwarfare, which we saw during the Russia-Georgia war in 2008 and the Israel-Hamas conflict (Operation Cast Lead) in January 2009. There has never been a single act of cyberterrorism, although I expect to see that start to happen in another three to five years as radical groups become confident about the havoc that they could potentially create via cyberattacks.
HYPPONEN: One of the key problems we have in understanding this issue is the lack of understanding of the differences between different threats. Some of these attacks (and attackers) have nothing to do with each other, yet we seem to refer to them as one and the same. A criminal who wants to steal your credit card information has nothing to do with an activist who wants to DDoS a corporate website as a protest. And neither of them has anything to do with a government employee launching cyberespionage attacks to steal classified information of foreign nations. All of these happen all the time. They have nothing to do with each other and cannot be solved with a single solution.
LIN: Everything in the media is [treated as] a cyberattack, and it masks important distinctions. Stealing information is a different kind of threat than destroying computers, and the public debate would be much saner if we distinguished between them.
ROOSENRAAD: One of the larger issues we have in the cybersecurity/Internet security/anti-spam/anti-bot/etc. industry…is the lack of a good common vocabulary. While this can sometimes just be annoying…the different terminology can actually hold back the fight against the Internet “bad guys.” There are very few organizations that can fight online threats on their own, and this means we need to share data and collaborate….But in order to work together, you need to be able to communicate. You need…a common lexicon.
WOODCOCK: These distinctions are very meaningful, and…[these categories are] far too often lumped together, in the way that people who don’t actually understand something will abstract it and refer to it as a cloud or a black box. Cybercrime is crime, some or all of which is executed online, but what’s interesting about it is that it’s crime, and that it’s the responsibility of law enforcement to investigate and prosecute it, to deter future crime. Cyberattack is a generalization of no great utility. Cyberterrorism is a boogeyman that’s possible, but doesn’t actually exist, and may not come to pass in our lifetimes. Cyberwarfare encompasses both cyberdefense, which is just good sense, and cyberoffense, which is cybercrime committed by governments. So each is a different thing with different actors: some individuals, some corporations, some governments, and others that are mythical or hypothetical….Abstractions and understanding by analogy…aren’t sufficient to guide action in this space.
ZUCKERMAN: DDoS has escalated to a serious problem for small web players and could possibly be very worrisome for mid-level government agencies. We’ve seen a high, growing level of attacks—particularly originating from the Chinese activist community—that systematically target the communication channels of human-rights NGOs. Do these attacks constitute cyberharrassment? Yes. Cyberespionage? Maybe. But cyberwar? No. War kills people.
Follow Ali Wyne on Twitter and Facebook.
Photo Credit: Palto/Shutterstock.com