China implanted tiny spy chips in servers used by Amazon, Apple
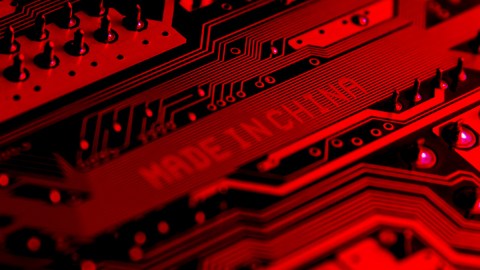
- A 2015 security test of a server sold by an American company found that someone in the supply chain had successfully embedded a tiny microchip on a motherboard.
- The company that manufactured the compromised motherboard provides servers to hundreds of international clients, including NASA and the Department of Homeland Security.
- U.S. officials linked the hardware attack to a People's Liberation Army unit, though it's unclear what, if anything, hackers have done or to what they have access.
The Chinese military was able to implant tiny malicious microchips on servers that made their way into data centers used by nearly 30 American companies, including Amazon and Apple, according to a new report from Bloomberg.
It’s a wide-reaching and potentially ongoing attack that likely gave Chinese actors unprecedented access to sensitive data belonging to American companies, consumers, government agencies and one major bank.
The Bloomberg report describes how, in 2015, Amazon Web Services had approached a startup called Elemental Technologies to help with the expansion of its streaming video service, Amazon Prime Video. During a security test of the servers Elemental Technology sold as part of its video-compression product line, testers discovered a rice-grain-sized microchip implanted inconspicuously on one of the server’s motherboards. The microchip wasn’t part of the original hardware design, so its existence could only mean one thing: Someone at some point in the supply chain had surreptitiously embedded the chip.
Americans officials, some of whom had already heard whispers of China’s plans to sabotage motherboards headed for the U.S., opened a top-secret and ongoing probe.
Hardware vs. software attacks
It’s hard to overstate how ideal it is, from the perspective of a hacker, to successfully conduct a hardware attack, which differs from a software attack in that it alters the physical components of a computer and not just its code. Joe Grand, a hardware hacker and the founder of Grand Idea Studio Inc., put it like this to Bloomberg:
“Having a well-done, nation-state-level hardware implant surface would be like witnessing a unicorn jumping over a rainbow,” he said. “Hardware is just so far off the radar, it’s almost treated like black magic.”
Even though the hidden microchips are tiny and hold small amounts of code, they pose outsized danger because hackers working from other computers can talk to the microchips and use them to gain access to networks and manipulate a server’s operating instructions, all without alerting security systems. But one downside to hardware attacks is that they leave behind a paper trail.
Tracing the attack
The servers sold by Elemental Technologies were assembled by Super Micro Inc., or Supermicro, the world’s leading supplier of server motherboards whose customers include NASA and the Department of Homeland Security. Supermicro is based in California but most of its motherboards are manufactured by contractors in China.
American officials traced the supply chain of the compromised motherboards and identified four Chinese subcontractors that had been building Supermicro motherboards for two years. After monitoring the subcontractors, the officials found that the microchips had been ordered, by bribe or threats, to be implanted on the motherboards by a specialized People’s Liberation Army unit.
“We’ve been tracking these guys for longer than we’d like to admit,” one official told Bloomberg.
American companies deny knowledge of the attack
Amazon, Apple and Supermicro have all denied knowledge of the attack or of the investigation.
“It’s untrue that AWS knew about a supply chain compromise, an issue with malicious chips, or hardware modifications when acquiring Elemental,” Amazon wrote. Apple said that it’s “never found malicious chips, ‘hardware manipulations’ or vulnerabilities purposely planted in any server.” And, perhaps unsurprisingly, the Chinese government didn’t acknowledge the attack, stating that “Supply chain safety in cyberspace is an issue of common concern, and China is also a victim.”
Despite the denials, 17 U.S. intelligence officials and company insiders, all of whom remain anonymous, confirmed the attacks to Bloomberg. Read the full report here.