Chart week – Internet safety
Today is the fourth day of Chart Week here at Dangerously Irrelevant. Today’s
post relates to the various technologies and procedures that public schools use
to protect students from inappropriate Internet material. All data are from the
recently-released NCES report, Internet Access
in U.S. Public Schools and Classrooms: 1994-2005
.
Technologies and procedures used by public schools to prevent
student access to inappropriate Internet material
Public schools have a variety of options when it comes to protecting students
from inappropriate material on the Web. As the chart below shows, nearly every
school is using blocking / filtering software. In addition, nearly every school
says that teachers or other staff members monitor student Internet usage.
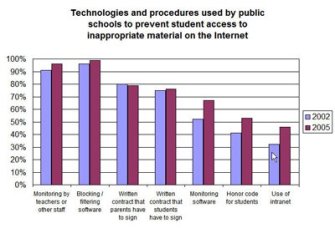
The federal data are unclear whether acceptable use policies (AUPs) are in
place in schools. What NCES asked is whether schools ask parents and students to
sign written contracts regarding Internet usage. About a fourth of schools in
2005 did not ask students to sign a contract and about a fifth of schools did
not ask parents to sign a contract regarding student Internet use. These
percentages were the same as in 2002. Elementary schools (72%) were less likely
in 2005 to have students sign contracts than secondary schools (88%). City
schools (72%) were less likely to have students sign contracts than rural
schools (82%).
It may be that schools have a student AUP in place but simply are not asking
students or parents to sign that they have read and understand the AUP. It also
may be that schools are relying on filtering / monitoring software and teacher
monitoring alone. Either way, all schools should realize that AUPs can be
powerful tools for school regulation and enforcement of appropriate Internet
usage and should not assume constructive notice
via student handbooks or school policy binders.
Other options employed by public schools to address student usage of the Internet include use of intranets to control student access, student honor codes, and monitoring software (e.g., keystroke logging and other surveillance software).
Schedule for the rest of the week
- Friday – professional development for use of the Internet in public
school classrooms