Why Syria Hacking Obama’s Twitter Account Is a Sign of Things to Come

Last week, the Syrian Electronic Army briefly hacked President Obama’s official Twitter account and claimed to have accessed some of his sensitive campaign emails. And this follows months of speculation that Chinese hackers have been doing everything from hacking into Mitt Romney’s 2012 presidential campaign to burrowing deep inside America’s most sensitive infrastructure. From an asymmetric warfare perspective, the Internet has tilted the military playing field once again. America has bombs, planes and tanks, the rest of the world has… free stuff on the Internet.
In other words, Syria couldn’t possibly attack the U.S. on our own soil (we hope), but it can mess with our Internet. As Syrian leaders have pointed out before, ever since the Syrian Electronic Army formed in 2011, these hackers have begun to comprise “a real army in a virtual reality.” Think of just some of the various attacks members of the Syrian Electronic Army have carried out over the past 18 months: they’ve hacked major media websites such as those of the New York Times and the Washington Post, they’ve defaced websites, coordinated denial of service attacks, sent false news accounts via social media accounts and used sophisticated phishing tacts to compromise the account information of potential opponents.
And they’re just getting warmed up. What if our national infrastructure is next? What if they decide to play a little game with our nuclear reactors (or, at least, those hooked up to computers and sensors), all while sitting thousands of miles away, playing around on the Internet?
It’s all eerily reminiscent of an earlier period of asymmetric warfare known as Vietnam. Remember when the U.S. thought it had the tanks, planes and troops to defeat a ragtag army in Asia? Look at how that turned out. Vietnam became a classic case of asymmetric warfare and gave rise to newer, deadlier forms of asymmetric warfare in which outmanned and outgunned guerrilla forces suddenly had a fighting chance against a much more powerful opponent. In 1975, the article “Why Big Nations Lose Small Wars” brought the term “asymmetric conflict” into the popular lexicon. The history of modern terrorism, in fact, can be thought of as a massive (and tragic) experiment in asymmetric warfare.
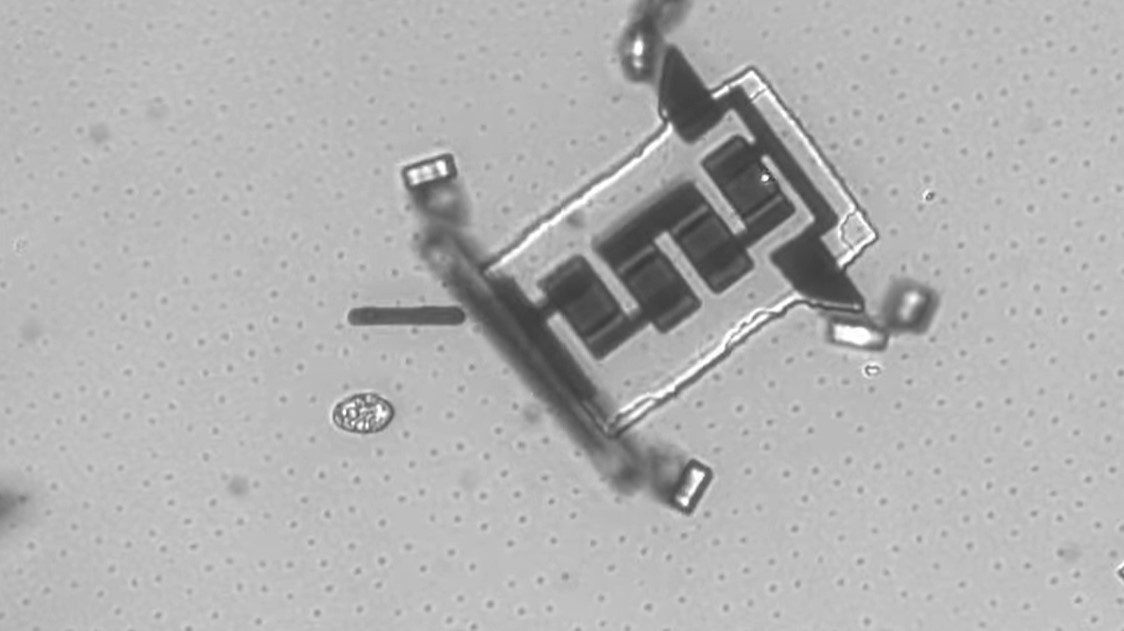
It’s no wonder that cybersecurity is getting so much attention these days. Universities are ramping up their cybersecurity training, federal agencies are desperately hiring the next generation of cybersecurity experts and top government officials are warning of a cyber “Pearl Harbor Attack” on U.S. territory. Already, municipalities such as Los Angeles are creating Cyber Intrusion Command Centers to fend off a potential cyber attack from a foreign actor that would cripple the city’s public infrastructure.
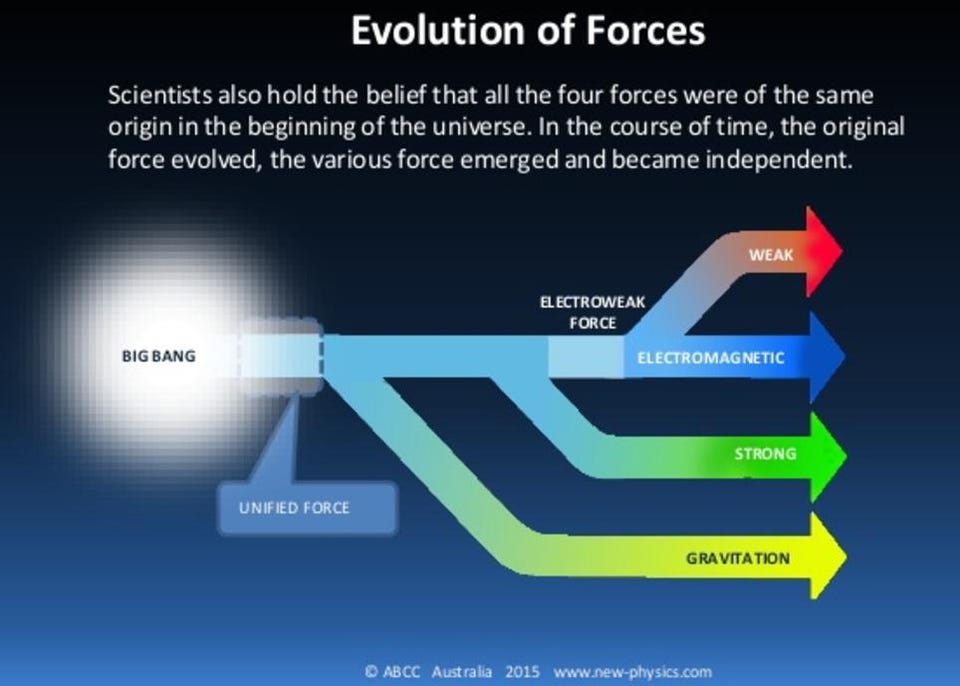
Every generation, then, the stakes in asymmetric warfare get ratcheted up. There are now entire books and manifestos written about topics like “the use of terrain as a force multiplier.” The Molotov cocktails turned into AK-47s, which then turned into IEDs and homemade dirty bombs. Then along came the Internet. The latest mutation in the asymmetric warfare arena – computer malware and viruses and hacks – may be the most pernicious for one simple reason: it brings the war home to Americans. All of a sudden, all of us are vulnerable. Each of us is connected to the Internet, and it’s only a matter of time before a few hour-long outages on Twitter or our favorite website turn into days-long outages of life’s essentials after our city’s infrastructure has been hacked. We have been warned.